

All 22 members of the National Science Board were terminated by the Trump administration via a terse email on Friday.
The administration has provided no explanation for purging the board, which helps steer the National Science Foundation and acts as an independent advisory body for the president and Congress on scientific and engineering issues, providing reports throughout the year. The ousters represent another severe blow to the NSF and the overall scientific enterprise in America.
Members received a two-sentence email saying that, "On behalf of President Donald J. Trump," their positions were "terminated, effective immediately."
Keivan Stassun, a professor of physics and astronomy at Vanderbilt University and director of the Vanderbilt Initiative in Data-intensive Astrophysics, was among those terminated. After reaching out to fellow board members and finding that they, too, had been terminated, he described the move to The Los Angeles Times as "a wholesale evisceration of American leadership in science and technology globally."
NSB members are appointed by the president and serve six-year terms, which overlap to provide continuity. Other members who spoke to reporters at Nature News told the outlet that the board was set to meet on May 5 and planned to release a report on how the US is ceding ground to China on scientific endeavors.
Assault on science
The NSF and the board were established by President Harry Truman in 1950. "We have come to know that our ability to survive and grow as a Nation depends to a very large degree upon our scientific progress," Truman said after creating them. "Moreover, it is not enough simply to keep abreast of the rest of the world in scientific matters. We must maintain our leadership."
The loss of all board members is just the latest attack on the NSF. Last year, the Trump administration proposed cutting its $9 billion budget by 55 percent, terminated hundreds of its active research grants, significantly slowed the pace of new grant awards, and laid off or forced out a massive chunk of its staff. Its director, a Trump appointee, resigned under the assault. Trump has nominated biotech investor Jim O’Neill, who lacks scientific expertise, to be the next NSF director.
Roger Beachy, a terminated board member, told Nature he was concerned about political interference and suspected the board may have been cleared out to make way for O'Neill's hand-picked members. The Trump administration has a track record of such moves. At the Centers for Disease Control and Prevention, anti-vaccine Health Secretary Robert F. Kennedy Jr. expelled all 17 members of an influential vaccine advisory board and replaced them with allies, who are largely unqualified but share Kennedy's anti-vaccine views. Trump also packed the President’s Council of Advisors on Science and Technology not with leading scientists and researchers but with tech billionaires, including leaders of Meta, Google, Oracle, and Nvidia.

In January 2026, during the height of protests against immigration raids in Minneapolis, federal agents shot and killed 37-year-old Renee Good. Before even gathering all the facts, the Department of Homeland Security labeled the mother of three an “anti-ICE rioter” who “weaponized her vehicle against law enforcement” in an “act of domestic terrorism.”
Days later, the feds announced a major expansion of “no-fly zones” in the name of national security. While such no-fly zones used to be about controlling aircraft, they now often focus on small drones. The expanded no-fly zones announced on January 16 prohibited such drones from flying within 3,000 lateral feet and 1,000 vertical feet of federal facilities.
But for the first time, the order extended no-fly zones to ground vehicles belonging to the Department of Homeland Security. Even while the vehicles were in motion. Even if they were unmarked. And even if their routes had not been announced.
This exceptionally ambiguous policy posed real danger to people like Rob Levine, a freelance photojournalist and commercial photographer in Minneapolis for nearly four decades. Since Levine got his remote-pilot certification and bought his first drone in 2016, he has flown a small fleet of DJI quadcopter drones to take aerial photographs and videos of Minnesota’s rivers, bridges, and cities, along with crowds gathered for outdoor concerts and parades. More recently, he has documented Twin City residents protesting the increased presence of federal agents in their community.
Levine immediately stopped flying when he saw the no-fly notice. The notice said government agencies could shoot down or seize drones “deemed to pose a credible safety or security threat,” and it warned of civil and even criminal penalties for drone operators.
“I saw what these federal agents were willing to do, the violence they were willing to visit upon even constitutional observers here in the Twin Cities who were just photographing what they were doing,” Levine told Ars.
Good’s killing had occurred just six blocks from his home. “It didn't take much imagination to think what they would do to somebody with a drone, and so for weeks I didn't go fly,” he said.
A week after the no-fly zone warning, the situation in Minneapolis escalated further when Customs and Border Protection officers killed Alex Pretti, a 37-year-old intensive care nurse, after wrestling him to the ground and shooting him multiple times.
Levine wanted his drones back in the air. But when he sought guidance from the Federal Aviation Administration, the agency candidly acknowledged that the no-fly zone warning was “ambiguous” and “therefore, any flight carries the risk of inadvertent violation.”
Could such a policy possibly be legal?
Hidden no-fly zones
The FAA had previously only advised that drone pilots avoid flying near "mobile assets" operated by the Department of Defense and Department of Energy, such as naval warships and truck convoys transporting nuclear materials between US national labs. But the “notice to airmen” alert in January—NOTAM FDC 6/4375—had created the equivalent of roving, 3,000-foot no-fly zones around federal agents’ cars and other vehicles operating in cities and towns across the country. And it didn’t just affect those trying to film federal agents. Because it was practically impossible to ensure compliance with the new flight restrictions, any drone pilot could be at risk during any flight.
“It created a whole lot of fear in the community,” said Vic Moss, CEO and cofounder of the Drone Service Providers Alliance, a drone industry trade association based in Lakewood, Colorado. In a post on March 11, Moss described the FAA flight restriction as posing an “impossible compliance problem” for drone operators, who could end up “ensnared inside a restricted zone with no way of knowing it.”
Drone pilots in the United States must use apps such as Air Control to seek official permission to fly in controlled airspaces. Any drones larger than 0.55 pounds must be registered with the FAA and have a Remote ID module that can “squawk” the drone’s identification and location at all times. That makes it easy for federal agents or authorities to see where drone operations are taking place. But the system provided no way for drone operators to avoid unmarked government vehicles in motion.
The no-fly zone restrictions were also exceptional in their length and scope. The FAA regularly issues temporary flight restrictions during natural disasters or to protect the airspace around government officials and sporting events such as professional baseball or football games. Most restrictions last just hours or days and cover specific geographic locations, according to the Electronic Frontier Foundation.
But the restrictions issued on January 16, 2026, would last until October 29, 2027—21 months—while covering many federal facilities and vehicles across the entire United States.
Pushing back
Given these unprecedented restrictions, the Electronic Frontier Foundation joined other members of the News Media Coalition—an international organization that includes more than 50 news organizations—in sending a letter to the FAA’s Office of the Chief Counsel.
The letter detailed “significant concerns regarding the FAA’s January 16, 2026 sweeping and unprecedented Temporary Flight Restriction.” It described the flight restrictions as violating the First Amendment by making it more difficult to record law enforcement officers. The letter also argued that the policy's ambiguity violated the Fifth Amendment to the US Constitution, which guarantees the right to due process before being deprived of liberty or property by the government.
Back in Minnesota, Levine spent weeks looking for lawyers who could help him challenge the FAA flight restriction as a freelance photojournalist—but he was racing against a deadline. One law firm alerted him that he had only 60 days to file a petition regarding the FAA decision. But he couldn’t find a law firm willing to back him.
“To me, this was an obviously unconstitutional rule by the FAA,” Levine told Ars Technica. “Even when I was looking for a lawyer, I had a lot of sympathetic ears, but nobody offered to take the case or to even help me with it.”
Levine eventually called a hotline for the Reporters Committee for Freedom of the Press, a nonprofit in Washington, DC, that offers free legal services. The organization took the case and filed a lawsuit, designated Levine v. FAA (26-1054), with the Court of Appeals for the DC Circuit on March 16.
They had barely beaten the petition deadline.
Partial relief
By March 16, it was common knowledge in the aviation industry that the FAA was aware of the issues and had prepared a revised version of its flight restriction notice, Moss said. But another federal agency was apparently holding up the revision. Many suspected that the agency responsible for the delay was the Department of Homeland Security (DHS).
“I think anybody with more than four synapses firing at the same time can realize that this was a DHS issue,” Moss said.
A Department of Homeland Security spokesperson told Ars only that "DHS routinely coordinates with the FAA on airspace restrictions to support operational security and safety of the Department."
On April 10, Levine and his lawyers pressed ahead by filing an emergency motion seeking to temporarily suspend the FAA flight restriction until the court had a chance to review the case.
That may have expedited the government’s next move. On April 15, the FAA removed the no-fly zones by replacing the sweeping flight restrictions with a “national security advisory” titled NOTAM FDC 6/2824. The revised notice dropped all mentions of flight restrictions and criminal charges. It instead “advised” drone pilots to avoid flying near “covered mobile assets” belonging to the Department of Homeland Security and several other federal agencies.
The revised notice was intended to “clarify drone operations based on user feedback,” according to an FAA statement shared with Ars. An FAA spokesperson confirmed that “the revised NOTAM removes the flight prohibition and instead advises pilots to use caution near protected operations while enabling federal security partners to assess and respond to potential threats.”
Levine and his lawyers were pleased. “First and foremost, our goal was to get the restriction thrown out so that Rob [Levine] and other journalists could be up in the air again,” said Grayson Clary, a staff attorney at the Reporters Committee for Freedom of the Press. “So on that front, we think this is already a victory.”
But Clary still plans to press ahead with the lawsuit.
“We're cognizant that the FAA is doing this because they don't want to have to defend what they did here on the merits in front of the DC Circuit, and we are going to fight back on that tactical gamesmanship,” Clary said. “We do plan to make clear to the DC Circuit that this shouldn’t have happened in the first place.”
The lingering chill
The new FAA advisory wording is "a lot better than it was," but it still comes off as "too ambiguous," according to Moss at the Drone Service Providers Alliance. He suggested that the Department of Homeland Security could handle any potential drone concerns rather than making it an FAA issue.
"If there's somebody harassing them with a drone, then I think there's other ways that can be dealt with," he said.
The FAA advisory is also potentially problematic because it still creates a “chilling effect to dissuade people from taking photos and videos, particularly of immigration enforcement agents, from the air,” said Sophia Cope, a senior staff attorney at the Electronic Frontier Foundation.
Like the earlier notice, the new advisory warns that federal agents can seize, damage, or destroy drones “deemed to pose a credible safety or security threat to covered mobile assets.”
"The threats that [drones] present to the national security and mission of DHS are evolving, and the approaches to securing the locations and personnel of the Department must also evolve," the Department of Homeland Security spokesperson said. "We ask that the [drone] user community respect the security of DHS operations, personnel and facilities and refrain from operating in vicinity of known enforcement activities, and all federal facilities."
The FAA advisory cites three existing laws as giving the federal agencies authority to seize or destroy drone threats.
But those laws first require federal agencies to have performed risk-based assessments to identify specific drone threats to the covered assets. It's unclear whether agencies have done those assessments, Cope said, and therefore, “they're just disincentivizing people from engaging in lawful, First Amendment protected activity.”
That chilling effect was very real for Levine while the initial flight restriction was in place. Hesitation cost him the chance to take aerial photos of protestors putting up roadblocks in his neighborhood to stop federal agents' vehicles toward the end of the US government’s Operation Metro Surge. Even when a friend asked him to help take drone videos and photos of a performance art event on February 28, he had to think hard about the risks.
As he tells it, “I eventually just screwed up my courage, as little as I have, and said ‘OK, I’m gonna do it.’”

In my misspent youth, I once worked a summer job as a waiter at Shoney's. It is an experience that I do not recommend. But it did teach me two valuable things: 1) How not to drown in a puddle of my own embarrassment when marching around the dining room with my fellow servers and singing a birthday song that began, "Happy, happy birthday, we're so glad you came"; and 2) That when the surly line cooks ran out of chicken fried steak, they would shout "86 the chicken fried steak!" through the pass.
To "86" something, in restaurant slang, is to say that it is out, finished, gone, through, not on the menu anymore. This is the only sense in which I have heard the term used in my entire life.
But according to Wikipedia, which naturally has an entry about the term, two further meanings do exist. "86" can also be applied to people a restaurant refuses to serve, and some slang dictionaries say it can refer to murder.
Which brings us to former FBI director James Comey, Instagram, and a picture of seashells.
86 the shells!
In 2025, Comey posted to Instagram an image of shells arranged in the shape of two numbers: "86 47."
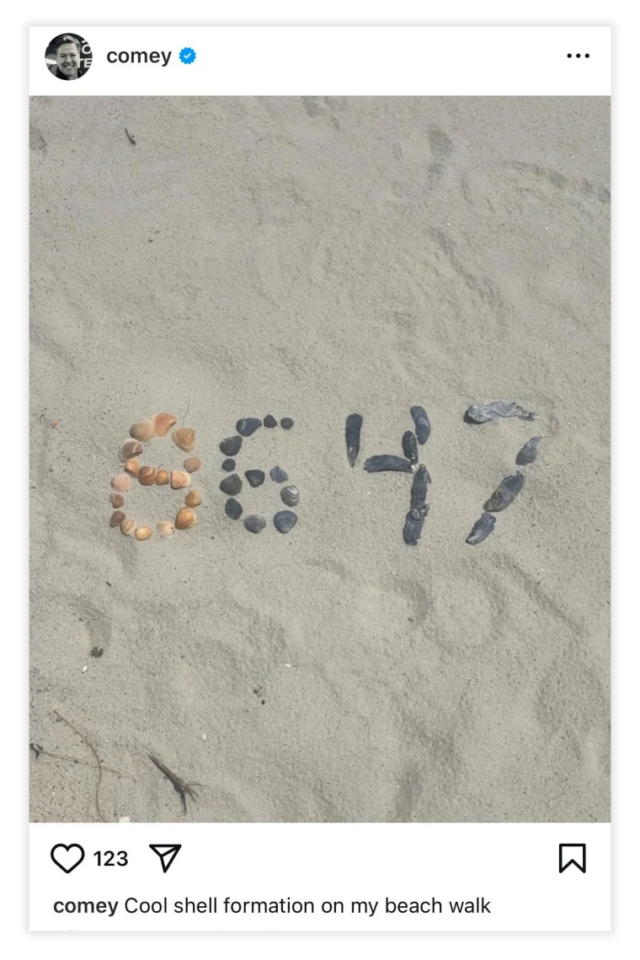 James Comey's seashell post.
James Comey's seashell post.
Trump, our 47th President, has long harbored a grudge against Comey, going back to Comey's investigation of Trump's possible Russian ties. Trump famously fired Comey in 2017—then, for good measure, fired his prosecutor daughter in 2025.
Trump has been clear for years about his desire to use the power of the federal government to make life more difficult for Comey, and federal officials in his second term have been willing to comply.
Fortunately, they have also been pretty stupid. Through a series of staggeringly incompetent actions, the administration already had its first Comey indictment tossed out in Virginia—a loss so epic that it got Trump's interim US attorney for Virginia booted, too.
Today, on completely new and unrelated charges, the Department of Justice has indicted Comey again, this time in North Carolina. The charge is nothing less than a threat to murder the president.
And it's all based on that single seashell image.
The new indictment says that Comey "did knowingly and willfully make a threat to take the life of, and to inflict bodily harm upon, the President of the United States, in that he publicly posted a photograph on the internet social media site Instagram which depicted seashells arranged in a pattern making out '86 47,' which a reasonable recipient who is familiar with the circumstances would interpret as a serious expression of an intent to do harm to the President of the United States."
You might expect more details in a case this serious and against such a high-ranking former official; there are none.
 The DOJ held a 15-minute press conference in which three men in suits tried to make this all sound normal and natural.
The DOJ held a 15-minute press conference in which three men in suits tried to make this all sound normal and natural.
Get in the clown car
A case this ridiculous, and about such a weighty matter, may be the bulbous red nose that completes the full-on beclownment of the Department of Justice under Trump. (The DOJ is currently run by one of Trump's personal lawyers.) Popular legal blog Above the Law, for instance, called today's move a "new low point for DOJ integrity."
As we have learned just in a single day, the federal government is willing to come after your broadcast licenses if you make a joke that Trump doesn't like... and your freedom if you make social media posts that Trump doesn't like. These are apparently the ways in which Trump is fulfilling his promise to halt government "censorship" of US citizens.
Trump himself is, of course, a famously peace-loving—sorry, "peace prize"-loving—man, most recently seen warning Iran that "a whole civilization will die tonight, never to be brought back again" in a social media post so unhinged even the pope had to step in and tell him to knock it off.
But apparently, it's James Comey's restaurant-slang seashell Instagram image that's the real crime, the sort of thing stopping America from being truly great again.

Earlier this month, Anthropic said its Mythos Preview model was so good at finding cybersecurity vulnerabilities that the company was limiting its initial release to "a limited group of critical industry partners." Since then, debate has raged over whether the model presages an era of turbocharged AI-aided hacking or if Anthropic is just building hype for what is a relatively normal step up on the ladder of advancing AI capabilities.
Mozilla added some important data to that debate Tuesday, writing in a blog post that early access to Mythos Preview had helped it pre-identify 271 security vulnerabilities in this week's release of Firefox 150. The results were significant enough to get Firefox CTO Bobby Holley to enthuse that, in the never-ending battle between cyberattackers and cyberdefenders, "defenders finally have a chance to win, decisively."
"We've rounded the curve"
Holley didn't go into detail on the severity of the hundreds of vulnerabilities that Mythos reportedly detected simply by analyzing the unreleased source code of Firefox's latest version. But by way of comparison, he noted that Anthropic's Opus 4.6 model found only 22 security-sensitive bugs when analyzing Firefox 148 last month.
The vulnerabilities identified by Mythos could have also been discovered either by automated "fuzzing" techniques or by having an "elite security researcher" reason their way through the browser's complex source code, Holley writes. But using Mythos eliminated the need to "concentrate many months of costly human effort to find a single bug" in many cases, Holley added.
By identifying bugs so efficiently, Holley writes that AI tools like Mythos tilt the cybersecurity balance toward defenders, who benefit when discovering vulnerabilities becomes cheaper for both sides. "Computers were completely incapable of doing this a few months ago, and now they excel at it," Holley writes. "We have many years of experience picking apart the work of the world’s best security researchers, and Mythos Preview is every bit as capable."
In an interview with Wired, Holley said that, from now on, this kind of AI-aided vulnerability analysis is something that "every piece of software is going to have to [engage with], because every piece of software has a lot of bugs buried underneath the surface that are now discoverable." And while it's possible that future models more advanced than Mythos may be able to find bugs that current models miss, Holley said he was confident that "at least on the Firefox side, having had a bit of a head start here, that we’ve rounded the curve."
Running through the AI-aided defense gauntlet could be especially important for the open source projects that underpin much of the modern Internet. That's both because their public codebases are easier for AI systems to explore for vulnerabilities and because many such projects rely on wildly insufficient volunteer maintenance for their security.
In a New York Times essay last week, Mozilla CTO Raffi Krikorian argued that the human difficulty of both finding bugs and writing complex software has created a kind of balance in cyberthreat research that Mythos could break wide open. "The programmer who gave 20 years of his life to maintain [open source] code that runs inside products used by billions of people? He doesn’t have access to Mythos yet. He should," Krikorian wrote.
Anthropic’s new Mythos AI model is raising concern among governments and companies that it could outpace current cyber security defenses, turbocharge hacking, and expose weaknesses faster than they can be fixed.
The San Francisco-based startup released a cyber-focused model this month, which has shown the ability to detect software flaws faster than humans but also demonstrated it can generate exploits needed to take advantage of them.
In one alarming case, the Mythos model showed it could break out of a secure digital environment to contact an Anthropic worker and publicly reveal software glitches, overriding the intention of its human makers.
This week, OpenAI also released its own advanced cyber model with similar capabilities.
The developments have led senior international financial officials and government ministers around the world scrambling to understand the dangers, in some cases seeking access to the new models that have only been given to a small number of vetted partners.
“This feels like the discovery of fire: a force that can profoundly improve our lives or, if mishandled, cause real harm across the digital world,” said Rafe Pilling, director of threat intelligence at cyber firm Sophos.
Last week, US Treasury Secretary Scott Bessent and Federal Reserve Chair Jay Powell summoned some of the largest US banks to discuss the cyber threats the AI model posed. The UK’s AI minister, Kanishka Narayan, told the FT “we should be worried” about the capabilities of the model.
These risks are well known within Anthropic. Logan Graham, who leads Anthropic’s frontier “red team,” which tests the lab’s models, said: “Somebody could use [Mythos] to basically exploit en masse very fast in an automated way, and most of the organizations around the world... including the most technically sophisticated ones, would not be able to patch things in time.”
AI tools have already significantly boosted the multibillion-dollar cyber crime industry. They have provided amateur hackers with cheap tools to write harmful software, as well as enabling professional criminals to better automate and scale their operations.
“Attacks are already increasing in frequency and sophistication, thanks to AI,” said Christina Cacioppo, chief executive at security and compliance firm Vanta.
“Most companies aren’t prepared to handle the risk because they’re still managing security through dated methods that are no match for the speed of AI-enabled attacks,” she added.
AI-enabled cyber attacks were up 89 percent in 2025 compared with a year earlier, according to data from security group CrowdStrike. Meanwhile, the average time between an attacker first gaining access to a system and acting maliciously fell to 29 minutes last year, a 65 percent acceleration from 2024.
“The game is asymmetric; it is easier to identify and exploit than to patch everything in time,” said one person close to a frontier AI lab.
Anthropic’s Graham said there were also internal concerns that companies would use Mythos to find “more vulnerabilities than they could hope to deal with in the near future.”
The heightened fears about AI and cyber security come amid signs that agents, which act autonomously on users’ behalf to conduct tasks, could also fuel a further rise in AI-enabled hacking.
Last September, Anthropic detected the first reported AI cyber-espionage campaign believed to be coordinated by a Chinese state-sponsored group.
It manipulated its coding product, Claude Code, to attempt to infiltrate about 30 global targets, including large tech firms, financial institutions, chemical manufacturers, and government agencies. It was successful in a small number of cases and executed without extensive human intervention.
Software researcher Simon Willison has warned there is a “lethal trifecta” of capabilities that arise with agents: access to private data; exposure to untrusted content, such as the Internet; and the ability to communicate externally.
Security professionals argue that the safest way to protect against cyber attacks when using an AI agent is to grant it access to only two of these areas. However, AI experts believe that much of the value from agents comes from granting access to all three.
“The bad news is that there is no good solution as of today,” said one person close to an AI lab. “The good news is [AI agents aren’t] yet in mission-critical settings like the stock exchange, bank ledger, or the airport.”
Stanislav Fort, a former Anthropic and Google DeepMind researcher who has founded AISLE, an AI security platform, said he was optimistic that AI could help to identify and fix a “finite repository” of historical security flaws.
To date, AI models have identified thousands of “zero-day” vulnerabilities—unknown weaknesses in commonly used software—some of which have been undetected for decades.
“We are gradually finding fewer and fewer zero days, of the worst kinds we can imagine,” said Fort.
Once these weaknesses were eliminated, the technology could be used to “proactively make sure nothing bad comes in [and] meaningfully increase the security level of the whole world as a result.”
Additional reporting by Kieran Smith in London.
© 2026 The Financial Times Ltd. All rights reserved. Not to be redistributed, copied, or modified in any way.

